PHP 8.2.9 Security Release Demonstrates Pantheon’s Commitment to Protecting your Sites
Image
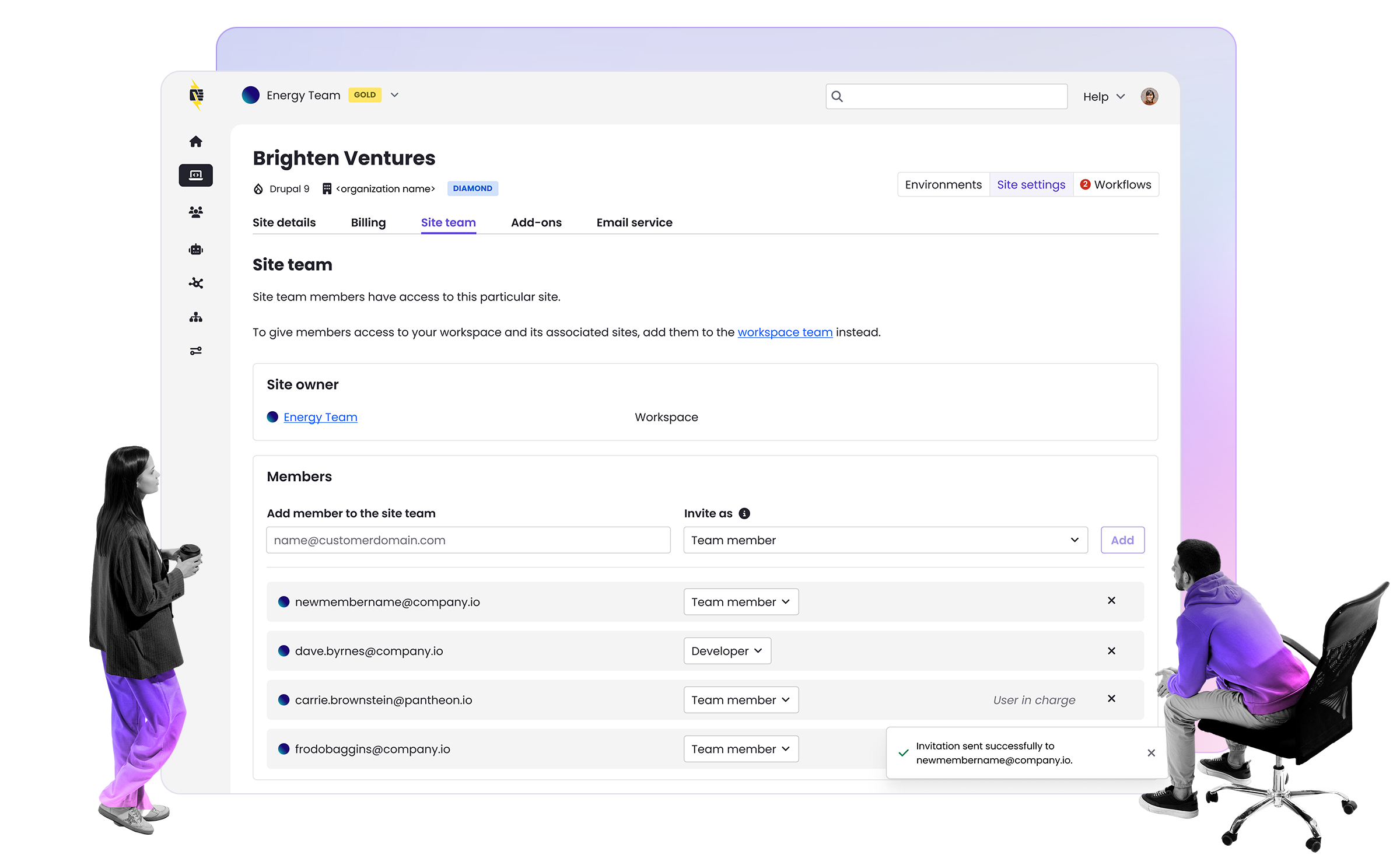
Pantheon has deployed PHP versions 8.2.9, 8.1.22, and 8.0.30 to customer sites running on the platform. These releases address vulnerabilities disclosed in CVE-2023-3823 and CVE-2023-3824. Although the PHP group rated these vulnerabilities “high” and “critical”, respectively, it is unlikely that either presented any significant risk to sites running on Pantheon both because of how the fundamentals of our security posture intersect with the details of these vulnerabilities.
How Pantheon's Architecture Increases Security
Some of the most common vectors of attack rely on overly-open file permissions. It is common, especially in the WordPress ecosystem, to set file permissions such that the CMS can update itself. There's a reasonable argument to be made that it is wise to let WordPress perform its own updates directly in the Live environment.
However, Pantheon sees that approach as an unacceptable security risk. Giving PHP code permission to change other PHP files is often exploited. Pantheon's architecture ensures that the only way to change version-controlled code on Test and Live environments is through our git-based deployment pipeline.
Similarly, it is common practice for some teams to use PHP's affordances that change PHP settings on a per-directory basis (through php.ini files) or similarly arbitrary schemes. Again, our experience tells us that the risks associated with that flexibility far outweigh the potential benefits.
Pantheon configures PHP settings in the same way for all sites. The amount of memory available to PHP and the size of the PHP cache increase with higher plan levels, and error reporting is more verbose in Dev and Multidev environments. Beyond that, “ini” level variables are locked down to a single, uniform set. But it is an unacceptable risk to let any given site, any given file and any given directory change PHP settings.
This fundamental security posture reduces the likelihood of exploiting sites on Pantheon.
Details on Latest PHP Security Vulnerabilities
Pantheon has a policy to update security vulnerabilities quickly. This is the most pragmatic way to avoid problems. The most recent vulnerabilities in PHP provide one example of the relative difficulty of exploiting unpatched vulnerabilities.
Vulnerability in XML Functions
The first vulnerability, CVE-2023-3823, relates to the way that the PHP XML functions manage the global state of the underlying XML libraries provided by the base operating system. The theory of this vulnerability is that a user might be able to use a specially-crafted XML file to read any file that PHP has access to. In order for this to work, though, the website must be using some module or plugin that allows the user to upload a file that is parsed with PHP’s XML functions. Even if this configuration exists on a site, the exploit still does not work unless some other library, such as ImageMagick, changes the state of the XML library globals before the XML file is parsed. This situation would be difficult for a user to contrive; however, it might arise naturally, by coincidence.
Vulnerability in Phar Executables
The second vulnerability, CVS-2023-3824, is marked critical because it can result in Remote Code Execution; however, exploiting the vulnerability requires using a specially-crafted PHP .phar file that the user would have to upload and run on the target site. Since a .phar file is itself executable code, this means that this vulnerability is only available to users who already have the ability to remotely run arbitrary code.
Have you Upgraded your PHP Version Yet?
If you are using PHP 8.2, 8.1 or 8.0, there is nothing further that you need to do. Pantheon has already updated your site to use the newest secure version of PHP. This is the primary benefit of using a managed WebOps platform: it allows you to stay focused on your development and marketing efforts, and not lose time taking care of server-related security vulnerability mitigation and similar maintenance.
If you are still on PHP 7.4 or earlier, though, you should schedule some time to upgrade to a supported version. While the vulnerabilities patched in these latest releases are not reported to affect PHP 7.4, the fact remains that there could be (and probably are) unpatched vulnerabilities in the end-of-life versions. Pantheon goes to great lengths to make it difficult for attackers to be able to make use of vulnerabilities that may exist in the software your site is running. However, the best protection is to keep your software up to date. PHP keeps getting faster, so there are also performance benefits to upgrading. PHP 8.2 is 15% faster than PHP 7.4.
See the documentation on Upgrading your PHP Version for more information.