Pantheon Now Enforces HTTPS by Default (Plus Really Simple HSTS!)
Image

Today I’m excited to announce that Pantheon enforces HTTPS by default. For quite some time, HTTPS has been included for all Pantheon sites, but you’d need to do some extra work to make sure your site isn’t accessible over insecure HTTP. That’s changed as of today, thanks in part to the magic of Pantheon’s upstream model. Now it’s easier than ever to implement best practices, make your site and your visitors more secure, and to boost SEO.
One-click Update for Existing Sites
For all new sites, HTTPS is now enforced out-of-the-box. For existing sites, apply the one-click update in the Dev environment. Make sure everything works as expected in Dev and Test before deploying to Live. You’ll want to ensure, for example, that you aren’t running into redirect loops and to remove any manual redirects from Drupal modules, WordPress plugins, settings.php, or wp-config.php.
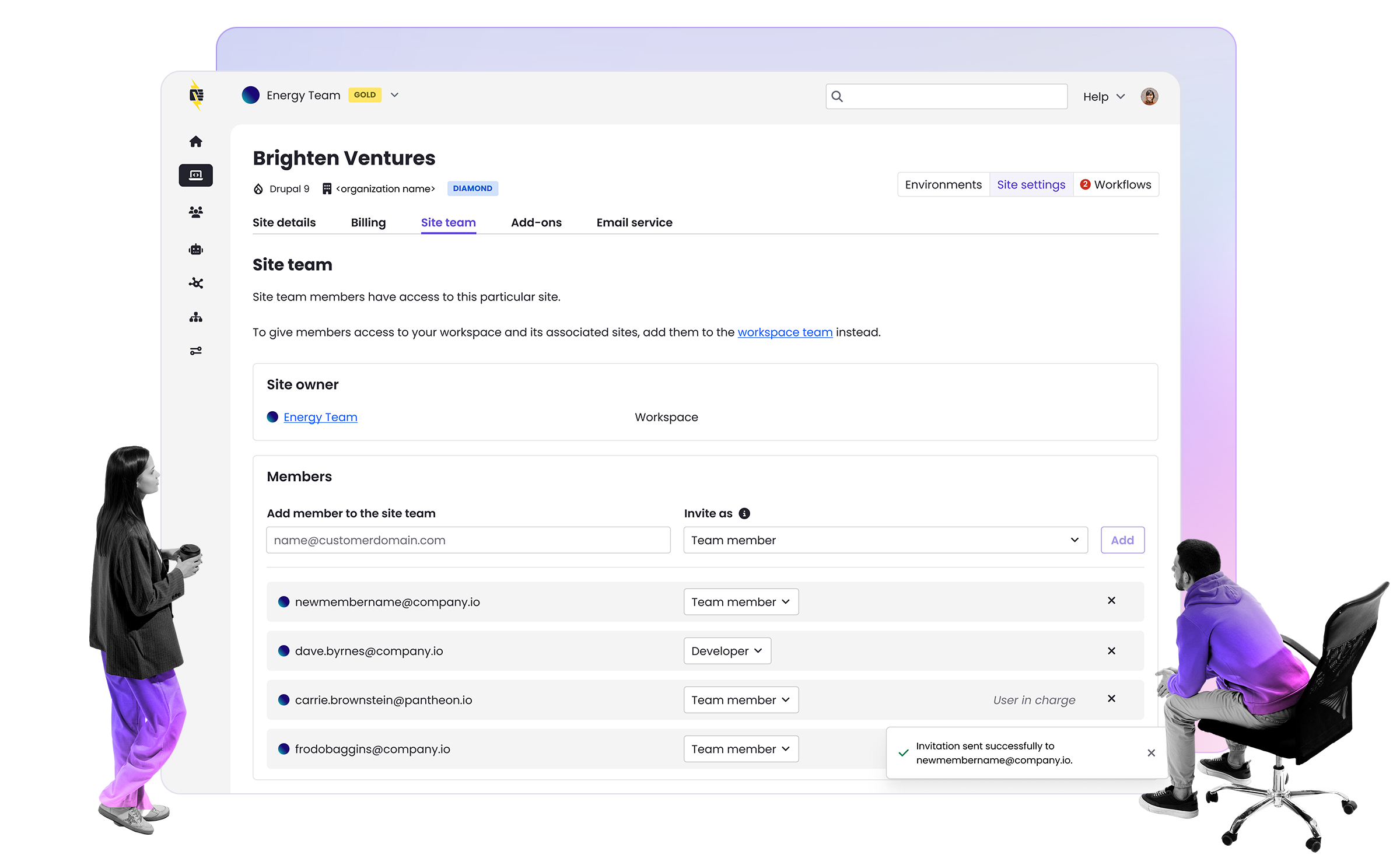
Choose a Primary Domain
As part of this release, you can now choose a primary domain, which will standardize all traffic on a single domain. So if you’ve added example.com and www.example.com to your site’s live environment and select www.example.com as the primary domain, when a visitor types in example.com into their browser they’ll be redirected to to https://www.example.com. Redirecting all traffic to a primary domain is a best practice to boost SEO. For more information on setting a primary domain see our Launch Essentials Guide.
Enforcing HTTPS in Custom Upstreams
If you maintain an Upstream, you can make sure every site created from it defaults to enforce HTTPS by adding a single line to pantheon.upstream.yml:
enforce_https: transitional
That’s it! We recommend each downstream site use the transitional mode in the Live environment, which sends a short 5-minute HSTS header, before committing to the year-long duration required to get an A+ SSL Labs Rating (described below).
Really Simple HSTS for SSL Labs A+ Rating
It’s now simpler than ever to implement HTTP Strict Transport Security (HSTS), which helps to protect your site against protocol downgrade attacks and cookie hijacking. HSTS instructs web browsers to interact with your site using only secure HTTPS connections and never via insecure HTTP. HSTS for over a year is required to obtain an A+ rating from SSL Labs, the industry standard tool to analyze your HTTPS configuration.
For the most secure configuration, add a single line to your site’s pantheon.yml file in the root of the codebase. This will enforce HTTPS on all your domains and all of your subdomains, even subdomains not on Pantheon, for a minimum of 1 year. Before moving into the most secure mode, we recommend running in “transitional” mode in the Live environment for some time to make sure everything works as expected, as it is a commitment.
api_version: 1
enforce_https: full+subdomains
See our documentation on YAML configuration files for details on considerations and all configuration options.
Encrypt the Planet
We’d also like to highlight our use and sponsorship of Let’s Encrypt and that we share in their mission to create a more secure and privacy-respecting Web. That’s why all Pantheon sites include automated HTTPS at no extra cost. Let’s Encrypt has accelerated adoption of HTTPS and is now the most popular certificate authority with the largest number of active certificates and the most widespread use. They recently started an individual-giving campaign to “Encrypt the Planet” so if you share in that mission consider donating to Let’s Encrypt.
HTTPS, HSTS, SSL Labs A+, Oh My!
Don’t sweat the acronyms. This is part of our effort to make it easier than ever to implement best practices, so you can focus on making sure your website drives business results.